PEGASIS, Piconet and Tunneling Protocol
November 3, 2016
Categorised in: Data Communicaiton & Wireless Sensor Networks
PEGASIS based on the assumption that all sensor nodes know the location of every other node.
Any node has the required transmission range to reach the BS in one hop, when it is selected as a leader.
The goal of PEGASIS are as following
- Minimize the distance over which each node transmit
- Minimize the broadcasting overhead
- Minimize the number of messages that need to be sent to the BS
- Distribute the energy consumption equally across all nodes
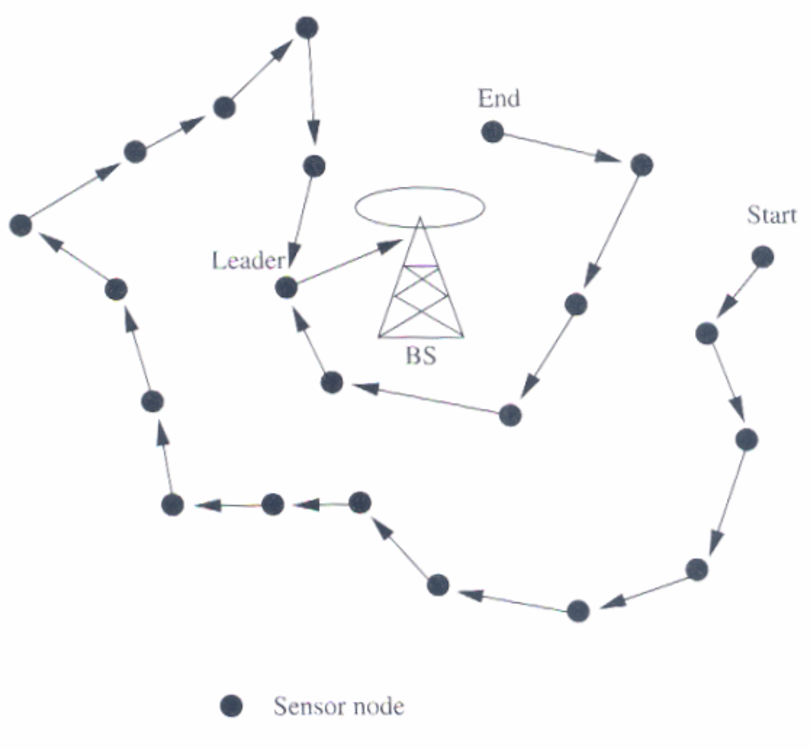
To construct a chain of sensor nodes, starting from the node farthest from the BS. At each step, the nearest neighbor which has not been visited is added to the chain.
It is reconstructed when nodes die out.
At every node, data fusion or aggregation is carried out.
A node which is designated as the leader finally transmits one message to the BS.
Leadership is transferred in sequential order.
The delay involved in messages reaching the BS is O(N)
Data gathering with PEGASIS

PICONET
Embedded Mobile NetworkingEmbedded Mobile Networking
There already exist many simple communication devices around our everyday life:
–phone, fax, copy machine
–printer, portable computer, PDA
–electronic access control to buildings and roads
–banking machine
–public information terminal, etc.
Imagine how much we may benefit if these devices can TALK with each other.
Benefit of Embedded Networks
Embedded Network:
–a small, wireless, portable communication device
–can be embedded in many communication devices
- and thus connect them together
Enhanced personal connectivity
–we have a multitude of connections to many devices
Context awareness
–the connectivity differs as we move around
Piconet of ORL
Developed by ORL (Olivetti and Oracle Research):
–general purpose
–low powered
–ad-hoc radio
Can talk to a multitude of computing and communication devices:
–static, mobile, or embedded
–used for sensing, communication, and control
–to support only a “base level” of connectivity between things.
Technological Choices of Piconet
ubiquitous
–periodically convey its state to others
–indoor or outdoor, exposed or embedded, line-of-sight or diffused
low-power, low-rate, low-range
–sleep (switched off) most of the time
radio-based
–IrDA (infrared) was not chosen as its inappropriateness in outdoor use
Prototype Piconet Hardware
major components:
- radio
- protocol
- runtime environment
- attribute store
Radio
418 MHz FM transceiver
around 5 meters of transmission range
- low-powered and cheap
- greater re-use of radio channel
- close to human’s definition of “proximity”
Protocol
ad-hoc, without base station
for short-lived transaction, not long-lived stream of data
4b6b DC balanced encoding
support 2 kinds of multicast:
- well-known (pre-assigned)
- transient (dynamically created)
Runtime Environment
on-board kernel
- a message queue
- a scheduler
on-board loader
Attribute Store
In Piconet, each node is responsible for describing itself to the rest of the world.
–any other node is thus able to determine what kind of services is provided by the device.
A mapping between a device’s name and service type should be supported.
–called “attribute store” in Piconet
Application #1: Pico + GPS in a Car

Application #2: Tour Guide

Tunneling Protocols
Tunnels
A fundamental building block for enabling security on the Internet
Encapsulating a message from one protocol P1 in another protocol P2, and using the facilities of P2 to traverse some number of network hops.
The encapsulation is stripped off, and the original message is reinjected into the network.
Example: IP packets can tunneled in several ways—IP over IP, PPTP
The extent of damage done by a tunnel depends on how routing information is propagated. If a tunnel does not leak a route info to outside, the damage is less.
IPIP tunnel
IPIP tunnel is a simple protocol that encapsulates IP packets in IP to make a tunnel between two routers. The IPIP tunnel interface appears as an interface under the interface list. Many routers, including Cisco and Linux based, support this protocol. This protocol makes multiple network schemes possible. IPIP tunneling protocol adds the following possibilities to a network setups:
to tunnel Intranets over the Internet
to use it instead of using source routing
SOAP – another tunnel
It can be used to wrap any arbitrary content over HTTP, a protocol permitted by many firewalls.
It is RPC over HTTP
HTTP Tunneling
SSH tunnel

Virtual Private Networks
Sites (individually protected via firewalls) with multiple locations may have to be linked privately via the public internet.
VPNs extend the boundary of a protected domain through the use of cryptography
Types: (i) Remote branch offices (ii) Joint Ventures (iii) Telecommuting
Remote Branch Offices
Organization with several branch offices that need to share resources securely as if they are on the same net
Define each remote security perimeter, and deploy firewalls, intrusion detection, and network monitoring. Establish VPNs between different locations—set up a firewall-to-firewall tunnel—using IPsec in tunnel mode to encapsulate IP packets
If the same IP address space is used in all offices, applications can use remote resources as easily as ones in the same physical location.
Pratik Kataria is currently learning Springboot and Hibernate.
Technologies known and worked on: C/C++, Java, Python, JavaScript, HTML, CSS, WordPress, Angular, Ionic, MongoDB, SQL and Android.
Softwares known and worked on: Adobe Photoshop, Adobe Illustrator and Adobe After Effects.
